Forging my way into an XFinity home network via the Arris TG862G
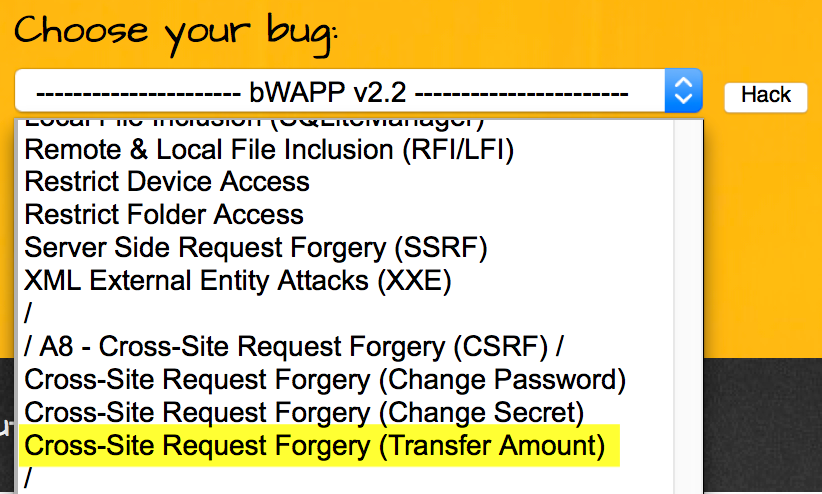
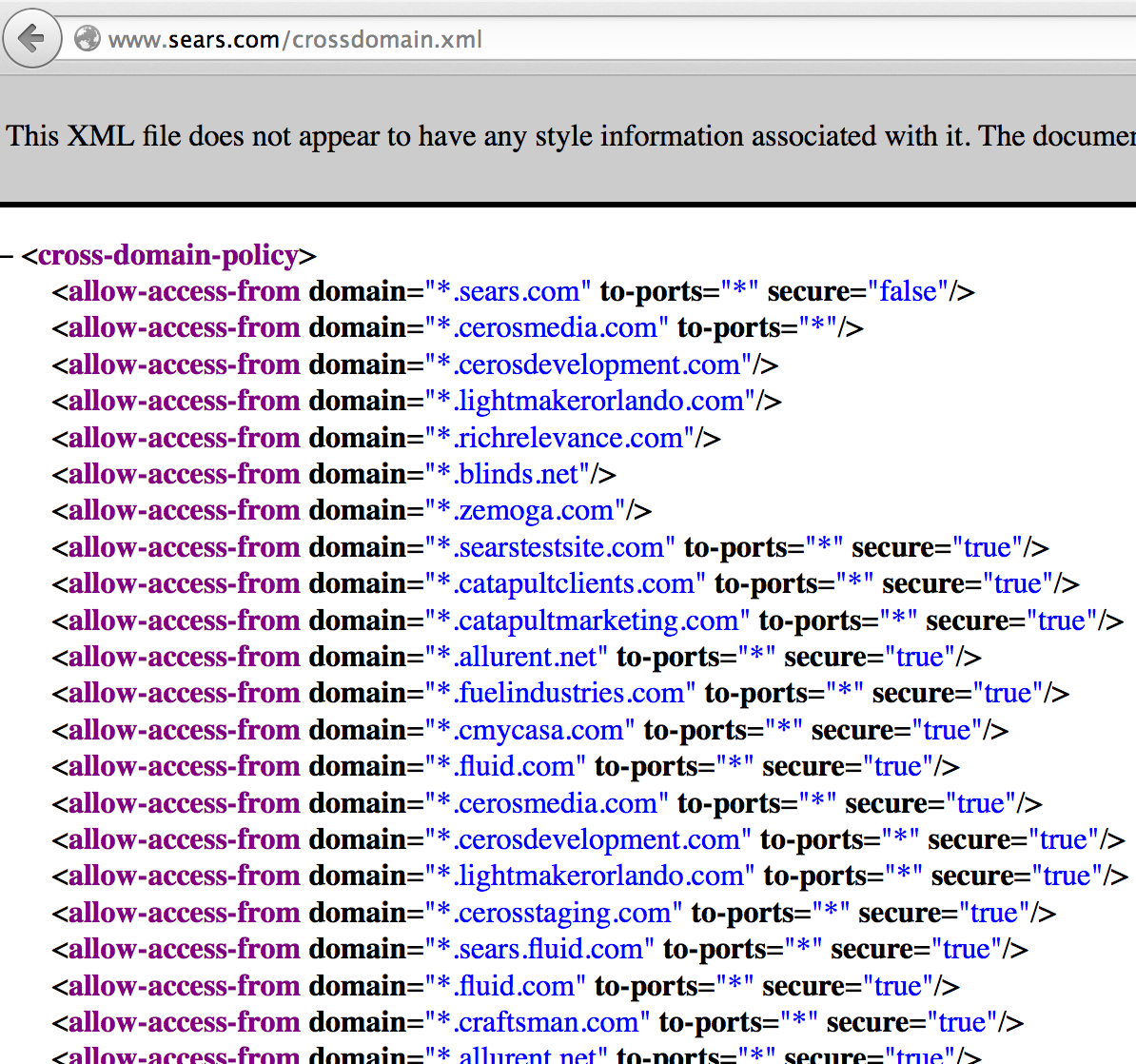
TL;DR: Using login CSRF + multi-stage CSRF, you can create a one click exploit that would silently log a user into their vulnerable, Comcast provided modem/router with default credentials (if they have not been changed) and then enable remote management (or anything else). I'll show how I did this with my previously vulnerable modem/router, and then give a more generic POC that you can try out on bWAPP, an intentionally vulnerable web application. Unnecessary Background This story starts about a year ago when my colleagues convinced me to stop being lazy and switch to a DOCSIS 3.0 modem so that I could actually get the speeds I am paying for. I filled out the Comcast XFinity form and had them send me a new modem. New toy -- Yay! So basically right after I had the new device working, I decided it was time to mess around. Turns out the modem is an Arris TG862G , a modem that is designed to be re-branded by many ISPs and distributed to their customers. Unfortu...